News
Grindr security flaw exposes user location data
the breach put more than three million daily users at risk

(Logo courtesy of Grindr)
More than three million of Grindr’s daily users were temporarily put at risk because of a major security flaw in the app that was exposed by a third-party site.
C*ckblocked, a now-defunct site that allowed Grindr users to view who blocked them by entering a Grindr user name and password, was able to access user information from Grindr’s Application programming interface (API). The information included email addresses, deleted photos, personal messages and the location of users.
Trever Faden, founder of C*ckblocked, told NBC that it would be easy for anyone to access a user’s private information.
“One could, without too much difficulty or even a huge amount of technological skill, easily pinpoint a user’s exact location,” Faden told NBC.
In a separate security issue, Faden claimed that Grindr users’ location, which must be inputed directly into the app and not via a third-party site, was not encoded and could be accessed by anyone monitoring public online traffic.
Faden emphasized that the ability to find a user’s location was “a feature, not a bug.”
NBC reports that two independent cybersecurity researchers confirmed the security flaw.
After Faden informed Grindr of the security issues, Grindr blocked the flaw that allowed third-party sites like C*ckblocked to receive data.
Grindr released a statement advising users not to use their username and password for other sites.
“Grindr moved quickly to make changes to its platform to resolve this issue. Grindr reminds all users that they should never give away their username and password to any third parties claiming to provide a benefit, as they are not authorized by Grindr and could potentially have malicious intent,” the statement reads.
However, Grindr denied that user location isn’t encoded.
“Grindr is a location-based app. Location is a critical element of our social network platform. This allows our users to feel connected to our community in a world that would seek to isolate us. That said, all information transmitted between a user’s device and our servers is encrypted and communicated in a way that does not reveal your specific location to unknown third parties,” Grindr’s Chief Technology Officer Scott Chen told the Huffington Post.
The company also released a statement on Twitter to inform users that the problems have been addressed and to be safe using their service.
As a company that serves the LGBTQ community, we understand the delicate nature of our users’ privacy. Ensuring safety and security of our users is of paramount importance to us and will continue to be our top priority. pic.twitter.com/vD2zXqxSr0
— Grindr (@Grindr) March 29, 2018
The flaw is similar to the one in the Facebook/Cambridge Analytica scandal, which allegedly exposed the personal data of 50 million users.
Maryland
Maryland’s oldest rural gay bar — and one of the last — is a log cabin in the woods
The Lodge is a Boonsboro watering hole resembling a log cabin

By SAPNA BANSIL | In the woods of a conservative Western Maryland town of fewer than 4,000 people is an unlikely landmark of state LGBTQ history.
The Lodge, a Boonsboro watering hole that resembles a log cabin, is Maryland’s oldest rural gay bar — one of a few remaining in the country, according to historians.
For about four decades, the Washington County venue has offered safety, escape and community to queer people far from large, liberal cities. Starting Friday night, The Lodge will close out Pride month with one of its biggest parties of the year: a weekend of dancing, drinking and drag in celebration of Frederick Pride, held about 20 miles away in the area’s largest city.
The rest of this article the Baltimore Banner published on June 27 can be read on its website.

South Africa National Assembly Speaker Thoko Didiza on June 17 swore in lesbian feminist Palomino Jama as a new MP.
Jama joins other LGBTQ legislators — including Public Works and Infrastructure Minister Dean Macpherson; Forestry, Fisheries and the Environment Minister Dion George; and Deputy Women, Youth, and Persons with Disabilities Minister, Steve Letsike.
Jama said she will work hard and excel as MP.
“What a great moment to be alive. Thank you youth of 1976, thank you Simon Nkoli, Phumi Mthetwa, Paddy Nhlaphos, Vanessa Ludwig, and others for what you did for the LGBTI people in the 80s and 90s. Lastly, for the fierce fist of the Jamas to always hit where it matters for the people of this country,” said Letsike.
Embrace Diversity Movement, a local LGBTQ organization, said Jama’s inauguration came at an appropriate time, during Pride month.
“Her swearing-in took place during a month of profound significance in June, which marks both international Pride Month and Youth Month in South Africa,” said the group. “Palomino is a seasoned queer activist and dedicated community builder with a distinguished record of leadership and service.”
“The EDM proudly supports Palomino in her deployment to parliament, her presence meaningfully advances youth and queer representation in public office,” added the Embrace Diversity Movement. “We are confident that she will serve the people of South Africa with integrity, courage, and distinction.”
South Africa is the only African country that constitutionally upholds LGBTQ rights. There are, however, still myriad challenges the LGBTQ community faces on a daily basis that range from physical attacks to online abuse.
Letsike in May faced a barrage of online attacks after she released a scathing statement against popular podcaster Macgyver “MacG” Mukwevho, who during a podcast episode in April insinuated that the reason behind popular socialite Minnie Dlamini’s “unsuccessful” relationships were probably due to the bad odor from her genitals.
Letsike, who viewed MacG’s comments as offensive, called for the podcaster to be summoned before parliament’s Portfolio Committee on Women, Youth, and Persons with Disabilities and criticized the local television station that aired the podcast.
X users and other social media subscribers bombarded Letsike with anti-lesbian comments. She, however, was unphased.
Letsike continues to face anti-lesbian comments, even though MacG apologized and the television station on which his podcast had aired cancelled its contract with him.
Israel
Activist recalls experience in Tel Aviv after Israel-Iran war began
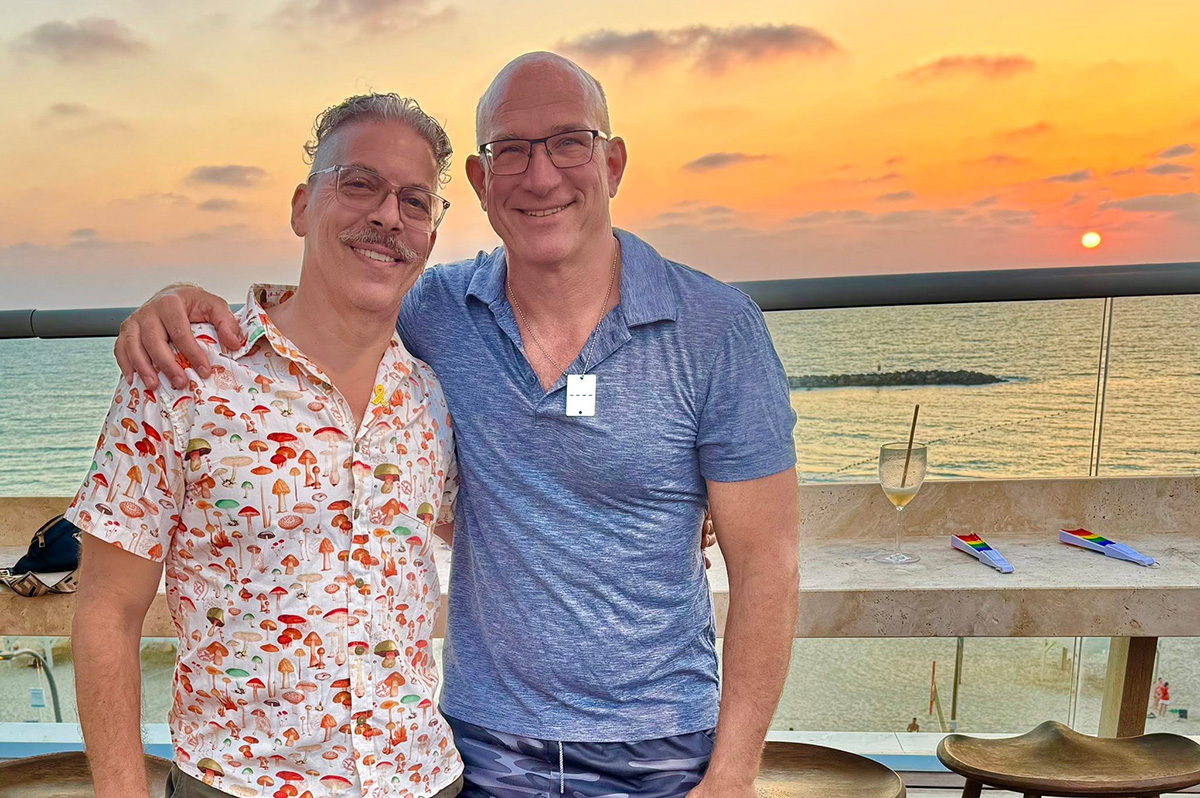
Marty Rouse was part of Jewish Federations of North America Pride mission

A long-time activist who was in Israel last month when its war with Iran began has returned to D.C.
Marty Rouse traveled to Israel on June 6 with the Jewish Federations of North America. The 5-day mission ended the night before the annual Tel Aviv Pride parade was scheduled to take place.
Mission participants met with Israeli President Isaac Herzog and several LGBTQ activists in Tel Aviv and Jerusalem. They visited the Western Wall, the Nova Music Festival site, and Nir Oz, a kibbutz in southern Israel that is less than a mile from the country’s border with the Gaza Strip. Mission participants also visited Sderot, a city that is roughly a mile from the Hamas-controlled enclave, a veterans rehabilitation facility, a new LGBTQ health center and the Aguda: The Association for LGBTQ Equality in Israel in Tel Aviv.
Hamas militants on Oct. 7, 2023, killed upwards of 360 partygoers and kidnapped dozens more at the music festival that was taking place at a campground near Re’im, a kibbutz that is roughly 10 miles southwest of Nir Oz. The militants killed or took hostage nearly a quarter of Nir Oz’s residents. They also took control of Sderot’s police station.

Tel Aviv Deputy Mayor Chen Arieli spoke at the mission’s closing party that took place at the Sheraton Grand, a hotel that overlooks Tel Aviv’s beachfront, on June 12.
Rouse and other mission participants planned to stay in Tel Aviv for the Pride parade, which was scheduled to take place the following day. He and Gordie Nathan, another mission participant who lives in Palm Springs, Calif., had checked into a nearby hotel that was less expensive.
“We said our farewells,” recalled Rouse when he spoke with the Washington Blade in D.C. on June 24. “We went to our hotels, and we get the warning, and then all hell broke loose.”
Israel early on June 13 launched airstrikes against Iran that targeted the country’s nuclear and military facilities.
Rouse said mission organizers told him and other participants who remained in Tel Aviv to meet at the Sheraton Grand for breakfast and dinner — Israel’s airspace was closed in anticipation of an Iranian counterattack, and authorities cancelled the Pride parade.
He said he went to bomb shelters at least twice a night for three nights.
Israel’s Home Front Command during the war typically issued warnings about 10 minutes ahead of an anticipated Iranian missile attack. Sirens then sounded 90 seconds before an expected strike.
Rouse and Nathan walked to the Sheraton Grand on June 13 when the Home Front Command issued a 10-minute warning. They reached the hotel in a couple of minutes, and staff directed them to the bomb shelter.
“You know to walk slowly, everything’s fine,” recalled Rouse. “You get 10 minutes, so everything was fine when the alarm goes off.”
Rouse described the Sheraton Grand shelter as “well lit” with WiFi, a television, and air conditioning. He was watching an Israeli television station’s live coverage of the Iranian missile attack when he saw one hit an apartment building in the Tel Aviv suburb of Ramat Gan.
A 74-year-old woman died and her boyfriend was seriously injured.
“I go over to look at the TV, just to watch,” recalled Rouse. “All of a sudden, you watch, and you see one bomb go and land and explode in Tel Aviv on TV. It landed and blew up.”
“I was like, okay, this is real, and so that was scary,” he added.
Rouse said the bomb shelter in the hotel where he and Nathan were staying after the mission ended was far less comfortable.
“It was dark. It was humid. It was hot. It was very uncomfortable,” said Rouse. “You really felt alone.”

Rouse and nearly everyone else on the mission who were in Tel Aviv when the war began left Israel on June 15. They boarded buses that took them to the Jordanian capital of Amman, which is a roughly 2 1/2-hour drive from Tel Aviv through the West Bank.
Rouse described the trip as “like a field trip” until they drove across the Jordan River and arrived at the Jordanian border crossing.
“You walk into this room, and instead of being in a well air-conditioned airport, you’re in this hot, humid, small place in the middle of the desert, packed with people, and those big, large, loud fans and pictures of military people on the walls,” he said. “It was almost like a Casablanca kind of feeling.”
Rouse said Jordanian authorities brought mission participants through customs in groups of 10. A Jewish Federations of North America liaison from Amman who previously worked as a tour guide for A Wider Bridge — a group that “advocates for justice, counters LGBTQphobia, and fights antisemitism and other forms of hatred” — went “behind closed doors” to ensure everyone was able to enter the country.
“It took a really long time,” Rouse told the Blade.

Mission participants arrived in Amman a short time later. They checked into their hotel and then had dinner at a restaurant.
“Now we feel like we’re safe and we’re in Amman,” recalled Rouse. “We’re sitting outside having a beautiful dinner.”
Iranian missiles passed over Amman shortly after Rouse and the other mission participants had begun to eat their dessert. They went inside the restaurant, and waited a few minutes before they boarded busses that brought them back to their hotel.
“No one was openly freaking out, which I was surprised by,” said Rouse.
The group was scheduled to fly from Amman to Cairo at 11 p.m. local time (4 p.m. ET) on June 16. They visited Jerash, an ancient city north of Amman, before their flight left Jordan.
“[The Jerash trip] actually took our minds off of everything,” said Rouse.
A Jewish Federations of North America contact met Rouse and the other mission participants at Cairo’s airport once their flight landed. Rouse arrived at JFK Airport in New York on June 17.
Trump-announced ceasefire ended 12-day war
President Donald Trump on June 23 announced a ceasefire that ended the 12-day war.
The U.S. three days earlier launched airstrikes that struck three Iranian nuclear sites. The ceasefire took effect hours after Iran launched missiles at a U.S. military base in Qatar.
Iran said the war killed more than 900 people in the country.
The Associated Press notes Iranian missiles killed 28 people in Israel. One of them destroyed Tel Aviv’s last gay bar on June 16.
The war took place less than two years after Oct. 7.
The Israeli government says Hamas militants on Oct. 7, 2023, killed roughly 1,200 people on that day when it launched its surprise attack on the country. The militants also kidnapped more than 200 people.
The Hamas-controlled Gaza Health Ministry says Israeli forces have killed nearly 55,000 people in the enclave since Oct. 7. Karim Khan, the International Criminal Court’s chief prosecutor, has said Israeli Prime Minister Benjamin Netanyahu and former Hamas leader Yahya Sinwar, who the IDF killed last October, are among those who have committed war crimes and crimes against humanity in Gaza and Israel.

Rouse upon his return to the U.S. said he “was never as aware of the comfort of another human being than I was during that time.” Rouse affectionately called Nathan his “bomb shelter boyfriend” and even questioned the way he reacted to the missile alerts.
“He’s sitting on the edge of the bed and he goes, okay, I’m going to put on my socks and my shoes, and I say, really? You’re going to put on your socks,” Rouse told the Blade. “The fact that I was nervous, that putting on socks might have changed the direction of our lives, to me was like I can’t believe I said that to him.”
Rouse quickly added Nathan helped him remain calm.
“If I was by myself, those nights would have been long enough,” said Rouse. “It’s a totally different feeling to be with another human that you know than to be by yourself.”
Rouse also praised the Jewish Federations of North America.
“JFNA really sprung into action and started to figure out all options to get us all safely home,” said Rouse. “It was all about logistics. Staff worked around the clock identifying and then mobilizing to get us back to the states. It was a great team effort and I know I speak for everyone in expressing our deep appreciation for their dedication to getting us safely home.”
-

 U.S. Supreme Court4 days ago
U.S. Supreme Court4 days agoSupreme Court to consider bans on trans athletes in school sports
-

 Out & About4 days ago
Out & About4 days agoCelebrate the Fourth of July the gay way!
-

 Virginia4 days ago
Virginia4 days agoVa. court allows conversion therapy despite law banning it
-

 Opinions5 days ago
Opinions5 days agoCan we still celebrate Fourth of July this year?












